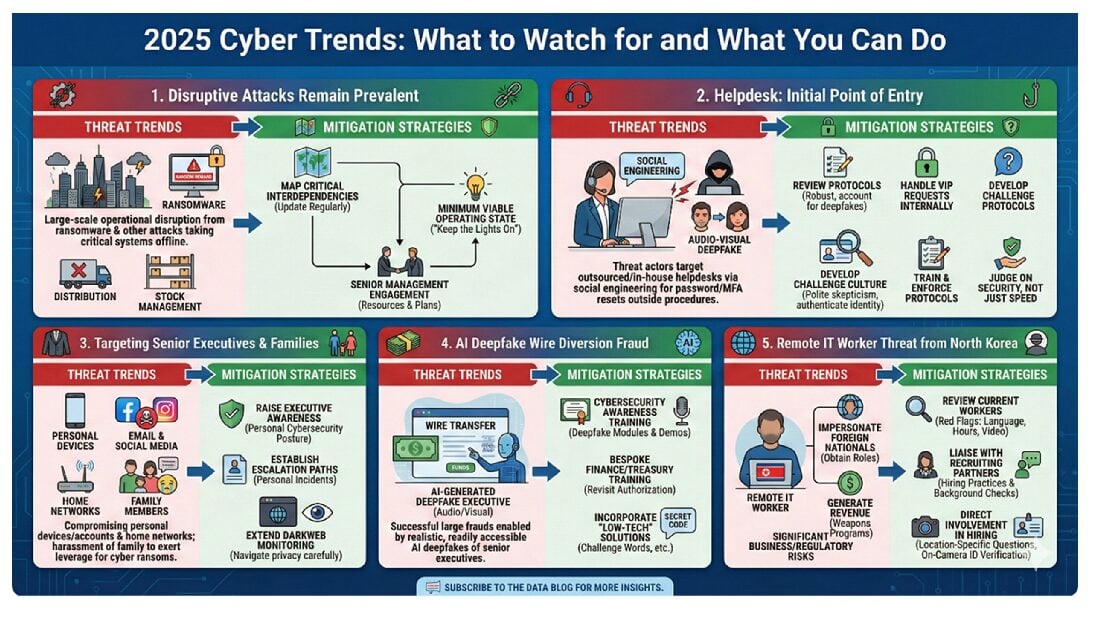
The cyber threat landscape in 2025 was varied with greater ebbs and flows in threat actor activity than in previous years. After a relatively quiet first half, cyberattacks ramped up in the second half of the year. These included major operational disruption in the United Kingdom at automanufacturer Jaguar Land Rover, exploitation of a zero-day vulnerability on the Oracle e-Business Suite leading to the reported compromise of dozens of businesses’ data, and the breach of a widely used Salesforce integration reported to have affected over 700 organizations. Earlier than expected, we also saw AI tools used not just to enhance, but also conduct, hacks. Anthropic discovered and publicly disclosed a state-sponsored attack designed and executed using autonomous artificial intelligence.
Against that backdrop, we outline in this Data Blog post five key trends we saw in 2025 and practical steps businesses may wish to take to address them.
1. Disruptive attacks remain prevalent. We continued to see large-scale operational disruption from ransomware and other attacks taking distribution and stock management systems offline.
Mitigation Steps to Consider:
A. Confirm that interdependencies for key control, distribution, stock management, and other critical systems have been mapped recently, and ensure those maps are regularly updated. It is extremely difficult, and sometimes impossible, to do this during an incident.
B. Identify what your minimum viable operating state would be if you were the victim of a disruptive attack, how that could be achieved (i.e., “how to keep the lights on”), and what resources would be required. Engage with senior management to ensure adequate resources are available and plans are in place that could be executed during an incident.
2. Helpdesks as the initial point of entry. Threat actors are targeting internal and external helpdesks (among other managed service providers) as a primary access vector, by socially engineering helpdesk staff into changing account passwords and resetting multi-factor authentication (“MFA”) tokens and devices outside of procedures.
Mitigation Steps to Consider:
A. Review helpdesk protocols for password/MFA reset procedures to ensure they are robust and account for the threat of audio-visual deepfakes. Additionally, consider handling requests from VIP users (e.g., senior executives, management, super users, and those with administrative privileges) internally.
B. Work with your helpdesk to ensure staff are trained and consistently follow protocols. This includes developing a “challenge culture” where helpdesk staff are encouraged to be polite yet skeptical of callers and require them to authenticate identity before assisting, irrespective of rank or circumstances. Ensure that helpdesk operations are not judged solely on metrics such as speed and lack of complaints, but also on enforcing security.
3. Threat actors are targeting senior executives (and their families). Threat actors are increasingly compromising senior executives’ personal devices, email and social media accounts, and home networks to exert greater leverage over businesses to pay cyber ransoms. This includes targeting family members—even minors—and deploying harassment techniques ranging from voice masking, sending executives photos of their children’s schools, to releasing compromising photos to colleagues and/or posting them on adult websites.
Mitigation Steps to Consider:
A. Raise awareness of this trend among senior executives and support them in improving their personal cybersecurity posture to better protect themselves, their families and the business. This should include informing them of how to escalate personal cyber incidents within the business. Some businesses are providing limited cyber services for senior executive and boards for their personal residence.
B. Confirm whether existing darkweb monitoring covers senior executives and consider working with them to extend it to do so if not. This should be navigated carefully due to privacy and data protection considerations.
4. Successful large wire diversion frauds have been enabled by audio-visual AI deepfakes. We have seen multiple wire diversion fraud schemes that leverage AI-generated deepfakes of senior executives. Barriers to entry are decreasing and the quality of (readily accessible) tools is increasing rapidly, significantly increasing the risk to businesses.
Mitigation Steps to Consider:
A. Ensure that general cybersecurity awareness training includes modules on the latest audio-visual deepfake technology, ideally with a demonstration of how realistic the technology is now, using a known individual from the business.
B. Provide bespoke training to, and revisit wire authorization procedures with, key members of your finance/treasury team(s). This can include incorporating challenge words and other simple but effective “low-tech” solutions.
5. The remote IT worker threat remains prevalent. Although U.S. authorities have disrupted parts of the North Korean remote IT worker scheme—whereby North Korean IT workers impersonate foreign nationals to obtain remote IT roles—the threat continues to evolve. Originally aimed at generating revenue for North Korea’s weapons of mass destruction and ballistic missile programs, the remote IT worker threat now includes ordinary foreign workers and a wider array of employees who outsource (parts of) their job or job tasks, and poses significant business, reputational, and regulatory risks for companies.
Mitigation Steps to Consider:
A. Review your current pool of remote IT workers for red flags associated with the remote IT worker scheme (e.g., individuals’ language skills day-to-day being poorer than alleged in interviews, working hours that diverge from those of the location where the individual purportedly works, limited appearance on video during meetings, etc.).
B. If you rely on outside recruiting partners, liaise with them to better understand their hiring practices and background checks. Consider more direct involvement in the hiring process, particularly for hires who will have access to critical systems. This can include updating interview protocols to require candidates to answer location-specific questions about the area in which they live and/or produce identity verification documents on camera.
***
To subscribe to the Data Blog, please click here.
The Debevoise STAAR (Suite of Tools for Assessing AI Risk) is a monthly subscription service that provides Debevoise clients with an online suite of tools to help them fast-track their AI adoption. Please contact us at STAARinfo@debevoise.com for more information.
The cover art for this blog post was generated by Gemini 3 (Nano Banana Pro).