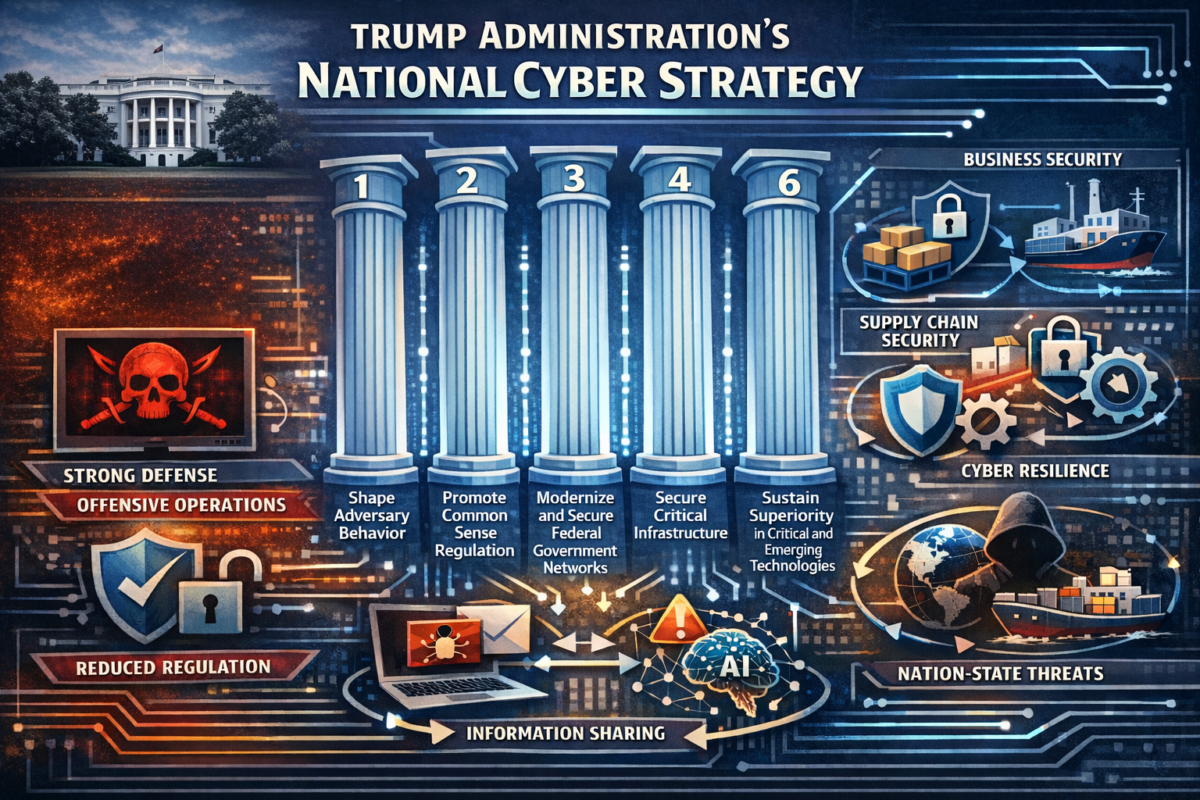
On March 6, 2026, the White House released President Trump’s Cyber Strategy for America (the “Strategy”), a directional statement of the Administration’s cybersecurity priorities. The Strategy signals an aggressive posture toward foreign cyber adversaries, a less prescriptive approach to cyber regulation, and a broader effort to protect U.S. technological and infrastructure advantages.
For businesses, this may mean that federal cybersecurity regulatory burdens ease. It may even mean companies reconsider long-settled questions against affirmative disruption by the private sector. However, expectations around cyber resilience, supply-chain security, and preparedness for nation-state threats are unlikely to diminish. In light of the Strategy, companies should consider reviewing nation-state threat assumptions, assessing supply-chain exposures, revisiting incident response and information-sharing processes, and factoring AI-related vulnerabilities into enterprise cyber risk management.
In this Debevoise Data Blog, we discuss the Strategy’s six policy pillars and explain what the Strategy means for businesses.
The Six Policy Pillars
- Shape Adversary Behavior. Adversary disruption is at the center of the Strategy. It provides that the United States will “deploy the full suite of U.S. government defensive and offensive cyber operations.” It also calls for incentivizing the private sector to “identify and disrupt adversary networks,” “creat[ing] real risk for adversaries,” and “impos[ing] consequences on those who … act against us.” In tone and emphasis, if not actual policy detail, this pillar signals the Trump Administration’s resolve for offensive deterrence, disruption, and pressure on hostile actors. Such disruption was previously successful when DOJ and U.K. law enforcement disrupted LockBit in 2024, leading to a noticeable drop in major incidents. If the administration can find additional opportunities it will be a welcome evolution in the cyber fight.
- Promote Common Sense Regulation. This pillar reflects a broader deregulatory impulse: cyber defense, in the Strategy’s view, should not devolve into a “costly checklist.” Instead, the Strategy favors lighter compliance burdens, clearer liability rules, and closer alignment between regulators and industry.
- Modernize and Secure Federal Government Networks. Federal information systems will be modernized through cybersecurity best practices, post-quantum cryptography, zero-trust architecture, cloud transition, continuous testing and threat hunting, and AI-powered security tools. The Strategy highlights procurement reform and removal of barriers to government adoption of the “best technology.” Although this pillar is directed at federal systems, it may influence procurement expectations, contractor obligations, and market demand for post-quantum, zero-trust, and AI-enabled security capabilities.
- Secure Critical Infrastructure. The Strategy emphasizes hardening critical infrastructure by focusing on operational resilience, supply-chain integrity, and strategic dependencies, while also favoring domestic products and vendors. It identifies services such as energy, financial services, telecommunications, data centers, water, and health care as key areas of concern. This pillar also suggests that state and local authorities should complement, rather than substitute, national cybersecurity efforts, signaling a preference for stronger federal control over critical infrastructure.
- Sustain Superiority in Critical and Emerging Technologies. The Administration sees cyber strategy as inseparable from technological competition, tying cyber policy directly to U.S. leadership in AI, quantum computing, cryptocurrencies, blockchain, and secure digital infrastructure. It calls for securing the AI technology stack, including data centers, adopting AI-enabled cyber tools, promoting agentic AI for defense and disruption, protecting AI data and models, and countering foreign AI platforms that censor, surveil, and mislead users. This pillar is therefore as much about industrial policy and strategic competition as it is about cybersecurity in the narrower sense.
- Build Talent and Capacity. The Strategy highlights the need for a talented cyber workforce as critical to implement the Pillars.
Key Takeaways and Considerations
Cyber and Privacy Deregulation Remains Aspirational for Now
The Strategy’s call to “streamline data and cybersecurity regulations” did not come with a proposal for how to address the current patchwork of state requirements and federal regulatory requirements on privacy and cyber. Notably, the Trump Administration has not signaled it would act to preempt state cyber and privacy laws, as it signaled with state AI laws. Previous efforts to enact national privacy legislation did not gain traction. While the Trump Administration wants to reduce compliance burdens, it also emphasizes the increasing risk of cyber threats, particularly from foreign adversaries. Prescriptive requirements around cyber controls may face opposition in light of the Strategy, but it is highly unlikely that regulations calling for cyber risk management and mature practices will be materially walked back.
An early test for the Strategy will come when the Cybersecurity and Infrastructure Security Agency (“CISA”) releases its final rule under the Cyber Incident Reporting for Critical Infrastructure Act (“CIRCIA”), targeted for May 2026. The Biden administration’s proposed CIRCIA rule would have been the most burdensome cybersecurity reporting requirement to date. It remains to be seen how the Trump Administration will shape CISA, and, in turn, rulemaking related to CIRCIA. For now, companies should assume that the compliance landscape may evolve unevenly rather than disappear.
Foreign Threats Are the Central Organizing Principle
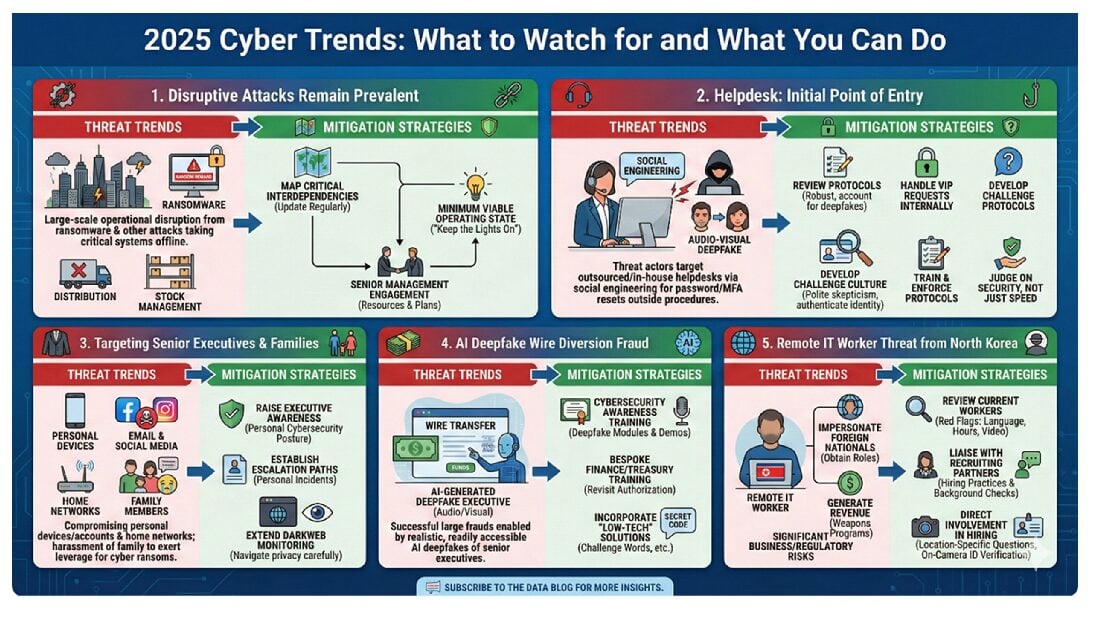
Consistent with the Trump Administration’s June 2025 Executive Order on cybersecurity and the Biden Administration’s National Cybersecurity Strategy, the Strategy reaffirms that nation-state actors represent the preeminent threat to U.S. cybersecurity. The Strategy calls for an assertive, offensive-capable posture to deter and respond to state-sponsored cyber activity and signals that the Administration views passivity and reactive defense as insufficient.
Businesses in sectors that intersect with national security—including telecommunications, defense contracting, financial services, energy, and health care—should expect continued and potentially heightened government focus on their exposure to nation-state threat actors. Companies should consider:
- Reviewing their threat models for indicators of compromise and attack patterns associated with advanced persistent threat groups linked to China, Russia, North Korea, and, in particular, Iran, given the ongoing military operations there;
- Enhancing supply chain security reviews to identify foreign-manufactured components or software, as well as state-sponsored remote work schemes, that could serve as attack vectors; and
- Solidifying their compliance posture under the Department of Justice’s Final Rule on Preventing Access to Sensitive Data, which restricts transfers of bulk sensitive personal data to countries of concern and which the Trump Administration has retained.
What Public-Private Cybersecurity Coordination May Look Like
The Strategy calls on the private sector to “identify and disrupt adversary networks and scale our national capabilities” and describes cybersecurity as a “collective effort” but does not describe what this collaboration between government and industry would look like. Is it possible that the Administration would allow companies to affirmatively reach out and “hack back”? Could companies seek to disrupt systems that pose a threat? Given that criminals and nation-states alike make heavy use of victim and other civilian infrastructure (and much of it in the enforcement jurisdictions of other countries) to carry out their exploits, companies should certainly proceed very cautiously in this area.
As noted above, CISA’s future is currently uncertain. As CISA’s role continues to evolve, businesses should monitor expansion or contraction of the agency, as well as new sector-based information-sharing mechanisms and any efforts to formalize expectations for private-sector disruption support or intelligence sharing.
AI as a Tool and a Target
The Strategy touts AI for its ability to dramatically accelerate threat detection, automate cyber defense, and enable faster, more scalable responses to attacks. At the same time, the Strategy recognizes that AI systems themselves present novel attack surfaces and can be weaponized by adversaries to conduct more targeted and sophisticated intrusions.
This dual framing echoes the June 2025 Executive Order’s acknowledgment that AI “has the potential to transform cyber defense by rapidly identifying vulnerabilities, increasing the scale of threat detection techniques, and automating cyber defense,” while also introducing new vulnerabilities.
As we have previously discussed, this dual nature means that companies cannot treat AI adoption and cybersecurity as separate workstreams. Key considerations include:
- AI as a cyber vulnerability: Companies deploying AI tools—whether proprietary models or third-party solutions—should incorporate AI-related vulnerabilities into their broader cybersecurity risk assessments. This includes risks arising from model poisoning, adversarial inputs, and the use of AI-enabled social engineering (e.g., highly convincing spear-phishing campaigns).
- AI for cyber defense: The Strategy signals that the Administration expects industry to invest in AI-powered defenses. Companies that have not yet evaluated AI-driven security operations tools, including for threat detection, log analysis, and incident response, should consider doing so.
- Vendor risk management: Given the complexity and variability of AI tools, companies should assess the cybersecurity posture of their AI vendors as part of a robust third-party risk management program.
Conclusion
Although the Strategy points toward a less prescriptive regulatory approach in some areas, it does not suggest a lower-expectation environment for cybersecurity. Instead, it reflects a national-security-oriented model in which foreign threats, infrastructure resilience, supply-chain integrity, and AI-related capabilities play a larger role in shaping both government priorities and private-sector expectations. Companies should therefore view the Strategy not as a reason to relax cyber and privacy programs but as a signal to reassess them against a more geopolitical and operationally demanding threat environment.
To subscribe to the Debevoise Data Blog, please click here.
The Debevoise STAAR (Suite of Tools for Assessing AI Risk) is a monthly subscription service that provides Debevoise clients with an online suite of tools to help them with their AI adoption. Please contact us at STAARinfo@debevoise.com for more information.
The cover art for this blog was generated by ChatGPT 5.4.