Last week, we wrote about a decision in which Judge Rakoff of the Southern District of New York denied the claim of defendant Bradley Heppner that documents prepared by Heppner using the consumer version of the AI model Claude for legal research were privileged. On February 17, 2026, Judge Rakoff issued a written opinion explaining the reasoning behind his February…
AI is disrupting a core assumption for companies entering routine business agreements: that their counterparty is not, and will not become, a direct competitor. Although non-disclosure terms and data use limitations have long been standard in many business-to-business contracts, compliance with these terms has rarely been a material concern, and enforcement has been reserved only for extreme cases that involve…
Avi Gesser has been recognized in Chambers Global Market Leaders: Artificial Intelligence, which highlights leading law firm lawyers advising on AI worldwide. Avi is one of only six lawyers ranked in the top AI tier in both Chambers Global Market Leaders and Chambers USA. In support of his ranking, clients note that Avi “leverages his deep regulatory and firm experience…
On February 10, 2026, Judge Rakoff of the U.S. District Court for the Southern District of New York ruled from the bench that documents a client created using a commercial generative AI tool and sent to his lawyer were not protected by privilege. Defendant Bradley Heppner was arrested on charges of securities and wire fraud on November 4, 2025.[1] During…
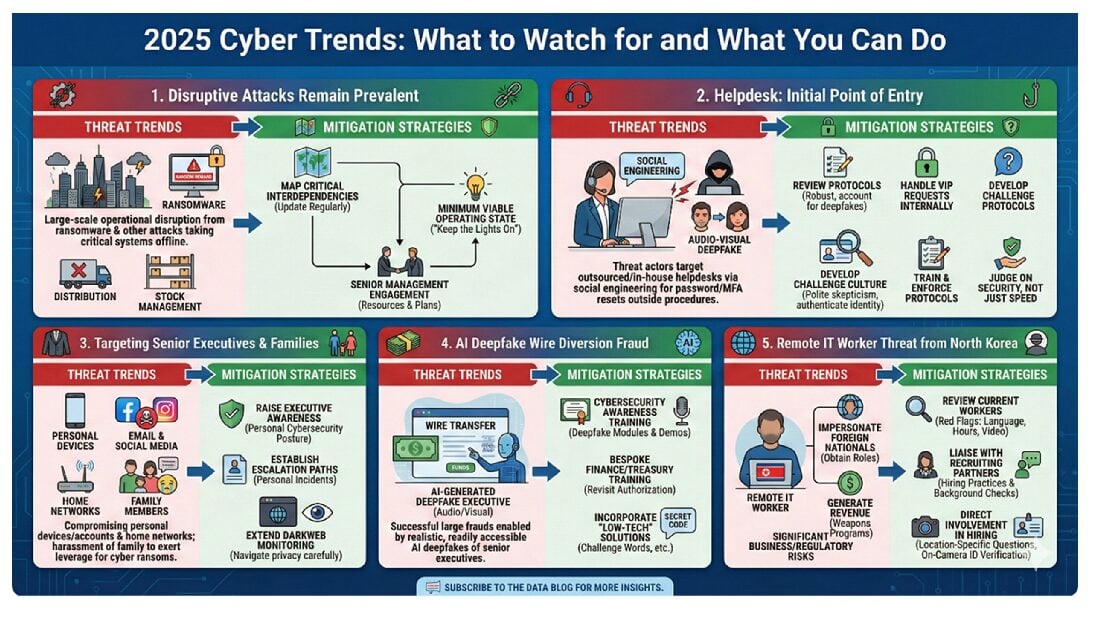
The cyber threat landscape in 2025 was varied with greater ebbs and flows in threat actor activity than in previous years. After a relatively quiet first half, cyberattacks ramped up in the second half of the year. These included major operational disruption in the United Kingdom at automanufacturer Jaguar Land Rover, exploitation of a zero-day vulnerability on the Oracle e-Business…