[vc_row][vc_column width=”2/3″]
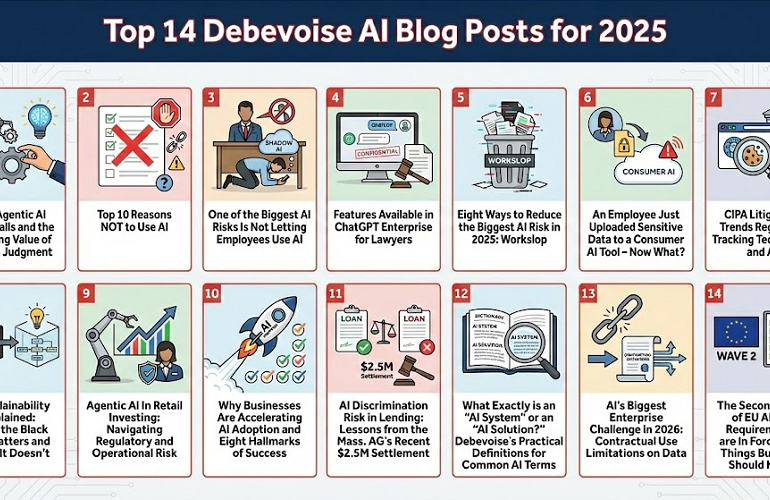
Cybersecurity incidents have become an ever-growing threat to companies as attacks become more sophisticated, particularly in the face of AI-enabled threat actors. When a cyberattack occurs, while the immediate focus… As generative AI platforms grow in sophistication, the initial era of text chatbots led by ChatGPT has evolved into a complex AI ecosystem of voice assistants and image and video… Why Agentic AI Often Fails and the Enduring Value of Human Judgment (11/4/2025) We’ve been doing a lot of work recently on agentic AI workflows. In this post, we share… The cybersecurity world has been in a state of alarm since Anthropic’s April 7, 2026, announcement of Claude Mythos Preview. And to many, the hysteria does not look like hype.… We are proud to share that a Debevoise team recently advanced to the final round of the inaugural GAR-LCIA Hackathon as one of four finalists. The recognition was awarded for… On April 17, 2026, the U.S. Attorney’s Office for the Eastern District of New York unsealed a 10-count indictment against Harish Chidambaran and Farhan Naqvi, the respective former CEO and…Latest